Today I interviewed my 10th candidate in 3 months for a security engineer role.
Anyone who’s done enough recruiting as a specialist in their field will know that (unless your organisation is constantly attracting a specific type) candidates often reflect the state of an industry.
If I were to go with trend, the first few candidates would indicate that a lot more ethical folk want to hack, rather than hacker folk wanting to be ethical.
So I figured something was wrong with the job advert we sent out. Try again.
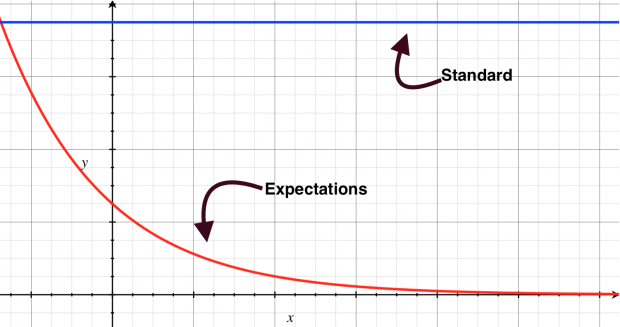
This time we actually got people who knew what nmap (a networking auditing tool) is! So we brought them in, gave them some coffee, made them comfy, and asked them unassuming questions about information gathering in a penetration test. With each subsequent candidate starting their answer with “Nessus”, my heart sank and the world looked like this:
We’re looking for more
I must stress at this stage that this is not their fault entirely. Of the countless years of experience they have, with hundreds of assessments they have done, they know to deliver a templated report that looks like a list of results from an automated scan. Their client expects it, which means their risk team is happy, everyone’s backs are covered and everyone gets paid. Happy days.
This is not what we are looking for. We want people who have ethically hacked systems to hack our systems.
The security engineer role at MoJ Digital and Technology has grown several heads since my last post. We expect a combination of consulting and architecting, with a massive entrée of penetration testing ability, preferably with a niche area of expertise in networking or crypto or web application development. Real stars in the field!
Changing our approach
So, we changed and adapted our approach. Apart from advertising on the usual places , we took to our intended audience; Hacker News, the International Association for Cryptologic Resource, IRC and forums, conferences, you know, where redditers, academics and technical people hang out. Did it work? Sort of.
We got a couple of fantastic CVs from Morocco and Sweden but the candidates weren't able to relocate. (Maybe that DMARC policy isn’t working as well as we hoped)
Not all was lost, though. We found some solid mid-level folk, with experience and understanding, who could’ve easily progressed to the senior role in a few months. But industry stepped in and scooped them all up because we all know how much more rewarding it is to secure an investment bank over the justice system (not!).
So what did we learn?
Easy lessons learnt:
- Do not lower your standards, even if you must lower your expectations.
- Design technical tests that are geared to show understanding over knowledge.
- Look for enthusiasm and logical ability above experience. Experience can be built, tunnel vision remains just that.
- Show interest in training your candidates and talk about opportunities to participate in conferences and meet-ups.
- Introducing telephone sifts as part of the process would save time at the interview stage.
- Civil service recruitment is a challenging operational process, especially when recruiting for specialists in high demand.
Harder lessons learnt:
Security-minded folk who can think originally still don’t think working for government (which is not all about intelligence agencies) is cool. And for good reason; some see government IT to be a massive legacy monolithic monster (partially true) where they will forever be in a dank corner, trying to troubleshoot memory issues in a some mid-90s middleware, and be valued by how many colour-coordinated reports they can churn out (not true).
It is up to us to give them the freedom to use their creativity, and put to use what they’ve traditionally done purely for the kicks. We need to incentivise these talented people with (nearly) free reign, explain the stakes to them, let them shape security practices in a department along the lines they feel comfortable.
Let them work flexible hours, let them work from (nearly) wherever they want. They already have the expertise to know what goes in a good policy and what broken guidance looks like. Let us show them how their efforts can make a difference.
If not, they can just win MoJ’s Capture the Flag event at this year’s 44con, and I’ll offer them a job* or failing that, a small prize.
And, I did hire the 10th candidate.
Come and visit us at this year's 44con introduce yourself and take part in our Capture The Flag.
*normal recruitment processes apply, I’m told.
1 comment
Comment by Justin Coleman posted on
Very interesting blog..... on so many levels! I hope the 10th candidate is settled and doing well?